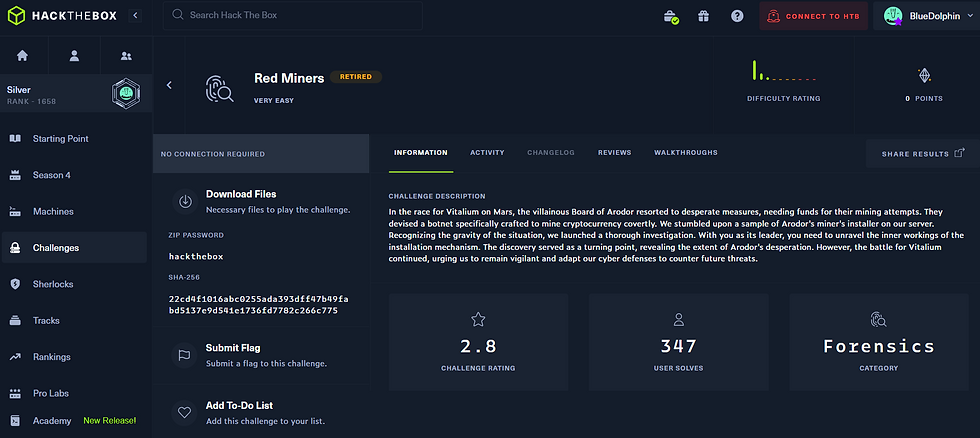
Hack the Box - Forensics - Red Miners
- BlueDolphin
- Mar 3, 2024
- 1 min read
CHALLENGE DESCRIPTION
In the race for Vitalium on Mars, the villainous Board of Arodor resorted to desperate measures, needing funds for their mining attempts. They devised a botnet specifically crafted to mine cryptocurrency covertly. We stumbled upon a sample of Arodor's miner's installer on our server. Recognizing the gravity of the situation, we launched a thorough investigation. With you as its leader, you need to unravel the inner workings of the installation mechanism. The discovery served as a turning point, revealing the extent of Arodor's desperation. However, the battle for Vitalium continued, urging us to remain vigilant and adapt our cyber defenses to counter future threats.
Solution Summary
Script analyses
Extract base 64 strings
Reconstruct flag
References
N/A
1) Script analyses
Script Analyses Summary
The script appears to be looking for IOC's related to crypto mining and attempts to remediate them. We see for example that the script checks for services, log files, and network connections related to crypto mining and then attempts to stop the processes, delete the logfiles, and close network connections.
We start by reviewing the provided challenge file "miner_installer.sh"
Initially when I saw the file name and skimmed through the file I felt like this might be related to a IAC (infrastructure as code) platform such as ansible, puppet, terraform and so on. But I quickly realized this script was actually enumerating the system for IOC's related to crypto mining in attempts to remediate these related IOC's.
The function "clean environment" caught my attention as it was removing files and changing permissions. This includes sensitive folders like the root users ssh key.
The following part of the script is now looking for specifics within the crontab.
In this area, we see the script is checking for processes related to crypto mining.
We continue to see the script is attempting to check processes related to crypto mining and kill the processes.
From here we see attempts to clean up log files related to crypto mining services which were identified by googling the IOC's found below.
3) Reconstruct flag
With the extracted base64 strings we are able to construct our flag as per the screenshot below where I leveraged Cyberchef to decode all four base64 strings to reveal our flag.
Browsing to our target web page reveals this landing page. The "secret facts" button in the top right is hiding our flag.
Browsing to "Secret Facts" provides us with a page and a message making it clear that only the administrators can access secrets. On the left side, we can see the burp request in which the Data Type is a string and that string is a secret. Attempting to pass the spooky and not spooky switch cases just moved me around the website and did not bring me closer to the secrets.
This is a strict comparison table to determine Boolean evaluations. It didn't really help me a whole lot other than realizing that perhaps the data type can be true and it will execute the use cases.
Sure enough changing the type to true evaluated as true and popped the first switch case. So if the secrets
We can see here that we didn't actually exploit a comparison variable, but passed the data type as true and the backend accepted this and revealed the first case which is 'secrets'. If secrets had been further down, this would not of worked.




















Comments