top of page

Search

THM Buffer Over Flow 1
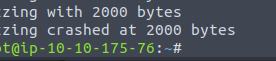
We will be tackling the vulnerable application for the THM buffer overflow challenge level 1. Configure Mona Mona is a script that helps...
BlueDolphin
Jun 27, 2021


HTB October
Summary This was a great machine involving guided routes for the initial access to the machine, without many rabbit holes. From here we...
BlueDolphin
Jun 26, 2021


HTB Canape
This machine largely involved the enumeration of a git repository and flask application running on a couchDB. Writing a python script...
BlueDolphin
Jun 23, 2021


HTB - Delivery
Overview This machine features an IT departments ticketing system that allows you to gain access by registering for a new account out of...
BlueDolphin
Jun 19, 2021


WireShark - Pico CTF - twoo twoo - 100 points
This was a fun pcap & wireshark challenge that involved a good initial investigation eventually leading to several HTTP files named...
BlueDolphin
Jun 17, 2021


Data Exfiltration with DNS
Data exfiltration is a constantly evolving threat. I wanted to dive in deep on exfiltration techniques such as DNS exfiltration.
BlueDolphin
May 31, 2021


Binary Exploitation - PicoCTF- Stonk - 20 points
This is my writeup for a format string vulnerability, that we exploit to read data off the stack.
BlueDolphin
May 26, 2021


justCTF 2020 - That's not crypto
This was a simple reverse engineering challenge, however because I am not a developer full time I had to pull in one of my team mates to...
BlueDolphin
May 9, 2021


What if SSH could VPN?
There is a handy tool that can allow anyone with a user level unprivileged SSH connection to create a VPN tunnel with little overhead....
BlueDolphin
Apr 25, 2021


OWASP Top 10 - OS Command Injection
Command Injection 101
BlueDolphin
Mar 14, 2021


HTB Tenten
This is a great machine that involves identifying WordPress vulnerabilities and leveraging burpsuite.
BlueDolphin
Mar 7, 2021


HTB Doctor
A machine featuring Server side template injection and exploiting Slunk Forwarders.
BlueDolphin
Mar 3, 2021


Jigsaw Ransomware Analyses
Jigsaw Ransomware Analysis In this blog we are analyzing Jigsaw ransomware through both static and dynamic approaches with the end goal...
BlueDolphin
Jan 16, 2021


HTB LaCasa De Papel
This machine was largely focused around using openssl to custom craft a malicious SSL self signed certificate to gain unauthorized access.
BlueDolphin
Jan 13, 2021


THM, Advent of Cyber2, Web Exploitation - Task 6
This challenge deals with cookie manipulation and encoding.
BlueDolphin
Jan 3, 2021


HTB Friend Zone
This machines forces critical thinking of DNS records and name lookups. With module injection to finish it off.
BlueDolphin
Dec 5, 2020


NA CTF - Forensics/Web & General
Newark Academy CTF (NACTF) is an online jeopardy-style cybersecurity competition hosted by Newark Academy's Computer Science Club. Form...
BlueDolphin
Nov 30, 2020


Hack the Box Frolic
Frolic had few open ports but many paths to exploitations. A ROP is required - be warned.
BlueDolphin
Nov 15, 2020


Hack the Box Nest
We get our foot in the door with open SMB shares and reverse engineer and encryption binary to take it all the way home.
BlueDolphin
Oct 26, 2020


Hack the Box Resolute
Resolute is a difficult but straight forward machine involving LDAP enumeration, and DLL injection.
BlueDolphin
Oct 12, 2020


Identity Access Management With Windows Server
Powerful tools and techniques to employ Identity Access Management with Windows Server Roles/Features
BlueDolphin
Sep 13, 2020


Google CTF 2020 Web Challenge - Pasteurize
This was the first Web Challenge from Google CTF, involving XSS and cookie stealing.
BlueDolphin
Sep 5, 2020


Hack The Box Forward Slash
This was a particularly hard machine that covered subdomain discovery, LFI, scripting, and reverse engineering.
BlueDolphin
Aug 31, 2020


CyBRICS CTF
https://cybrics.net/ CyBRICS is a computer security competition (CTF) organized in a cross-university effort by BRICS countries academia....
BlueDolphin
Aug 25, 2020
bottom of page